Advanced Cybersecurity Solutions for Digital Resilience
Protect your digital assets with our comprehensive cybersecurity ecosystem. From identifying hidden vulnerabilities to preventing real-time attacks, we provide multi-layered defense strategies to keep your data safe, compliant, and always available.
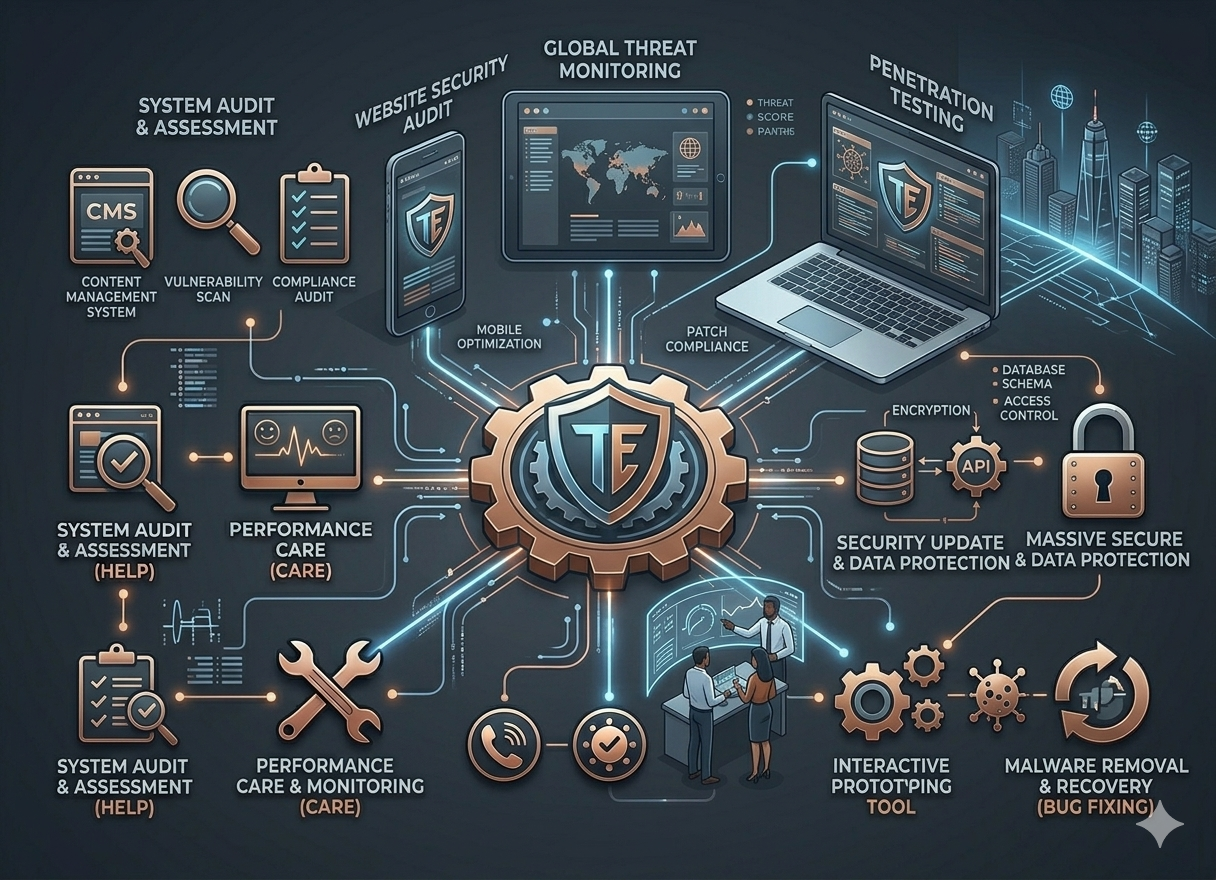
Strengthen Your Technical Perimeter
We combine human expertise with automated tools to uncover and eliminate security gaps before they can be exploited.
- Website Security Audit: Detailed assessment of your web architecture to find security loopholes.
- Penetration Testing: Simulating real-world cyberattacks to test the strength of your defenses.
- Malware Removal: Rapid identification and elimination of malicious scripts and unauthorized access.

Secure Foundations for Growing Businesses
Ensure your data remains private and recoverable with our enterprise-grade encryption and backup protocols.
- SSL Setup & Configuration: Encrypting communication between your server and users to prevent data theft.
- Data Backup & Recovery: Implementing automated backup systems for quick disaster recovery.
- Security Update & Optimization: Continuous patching of core systems to defend against emerging global threats.
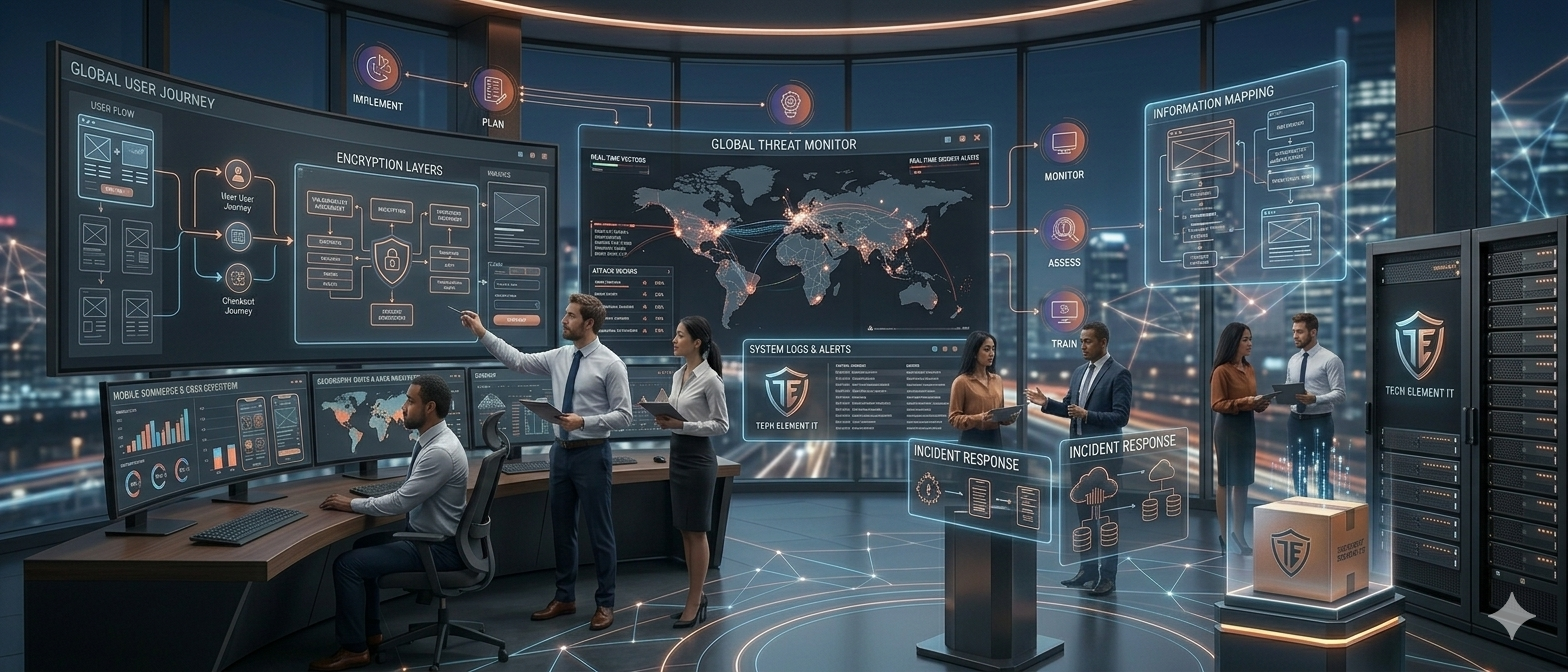
Strategic Cyber Defense Lifecycle
We follow a rigorous, circular security methodology to ensure your business stays protected against an ever-evolving threat landscape.
Plan (Digital Strategy)
Defining security goals and identifying the most critical assets that require maximum protection.
Monitor (Real-time Watch)
Implementing 24/7 surveillance tools to detect suspicious activities and unauthorized login attempts.
Assess (Vulnerability Scan)
Regularly auditing the entire infrastructure to find new technical weaknesses as your system scales.
Train (Security Awareness)
Ensuring that all human elements and protocols are aligned with the latest security best practices.
Implement (Defense Execution)
Deploying firewalls, encryption, and security patches to create a bulletproof digital environment
Our Impact in Cybersecurity
Explore how we have helped international clients secure their sensitive data and maintain 100% compliance. From fintech platforms to e-commerce giants, we’ve built fortresses around global digital identities.
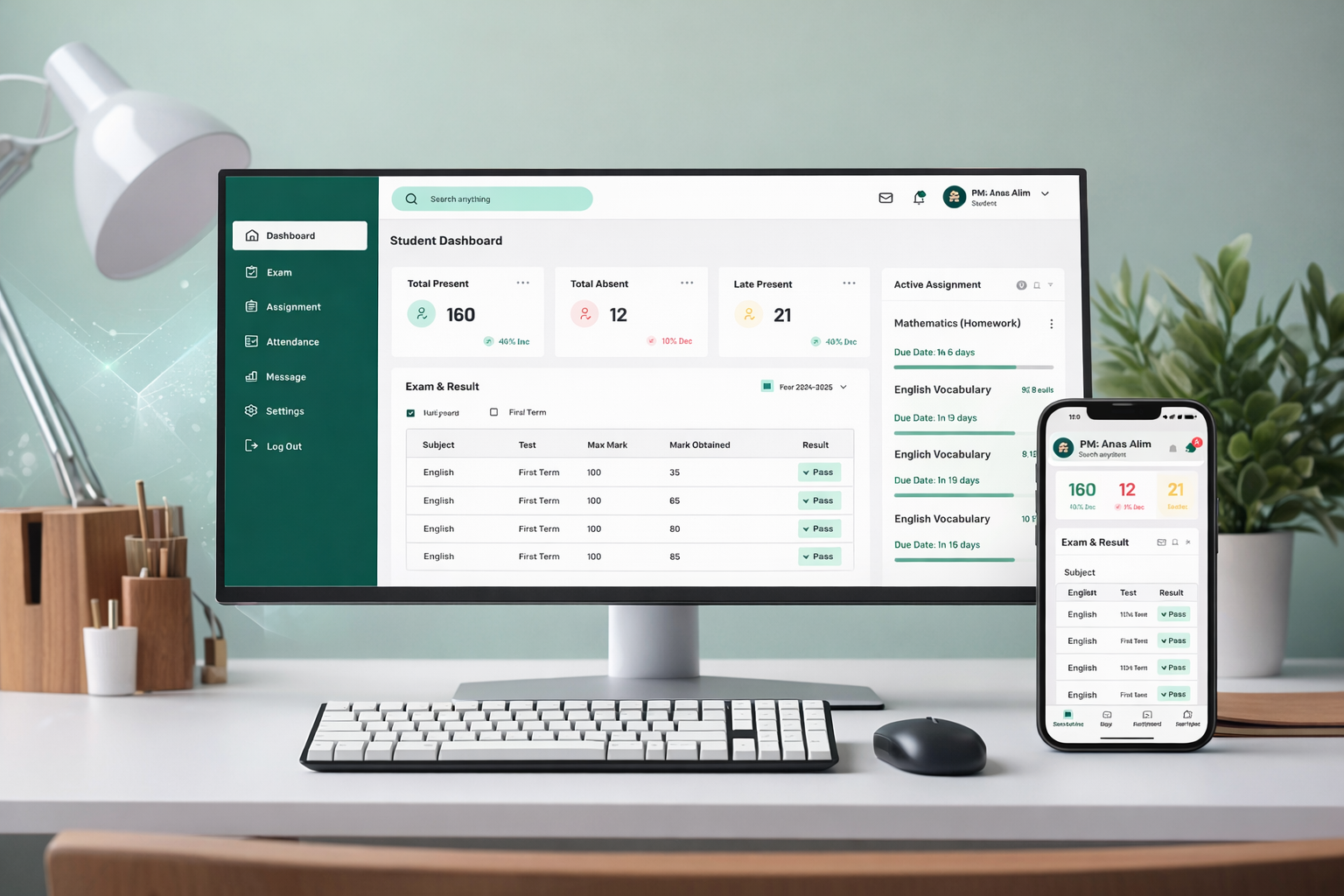

✔ Automated student management ✔ Improved efficiency by 70% Education ERP is a smart and centralized school management system designed to streamline academic and administrative operations. It automate...
Education ERP

e-Sales Hub Mobile App
e-Sales Hub Mobile App is a modern, scalable mobile commerce solution designed to help businesses manage and grow their online sales efficiently. Developed by Tech Element IT, the app enables vendors...
e-Sales Hub Mobile App

ProyojonShop Mobile App
ProyojonShop Mobile App is a powerful multi-vendor e-commerce solution designed to simplify online selling and enhance customer experience. Developed by Tech Element IT, the app enables multiple vendo...
ProyojonShop Mobile App


KRY International Mobile App is a modern, user-centric e-commerce mobile application designed to deliver a seamless digital shopping experience. Developed by Tech Element IT, the app enables users to...
KRY International Mobile App
Frequently Asked Questions
Got questions? We've got answers.
We recommend a full audit at least once every quarter, or whenever you implement significant updates to your software or server infrastructure.
Our "Data Backup & Recovery" protocol ensures we can restore your system to its last secure state immediately, while our malware removal team works to eliminate the threat and patch the entry point.
Yes, we handle the complete SSL setup and configuration process. This ensures that all data transmitted between your users and your server is fully encrypted and secure.
Absolutely. Our security audits and data protection protocols are designed to help your business meet global standards such as GDPR, SOC2, or HIPAA, ensuring your operations are legally compliant.
A security audit is a systematic review of your entire infrastructure for vulnerabilities, while Penetration Testing (Ethical Hacking) is a targeted attempt to actually bypass those defenses to see how they hold up under pressure.